Cisco ASA 8.4 Port Forwarding Port 25 with ASA 8.4 with ASDM
dp lexi_bunni
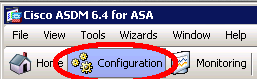
Step 1. Open ASDM and jumb to Configuration mode:

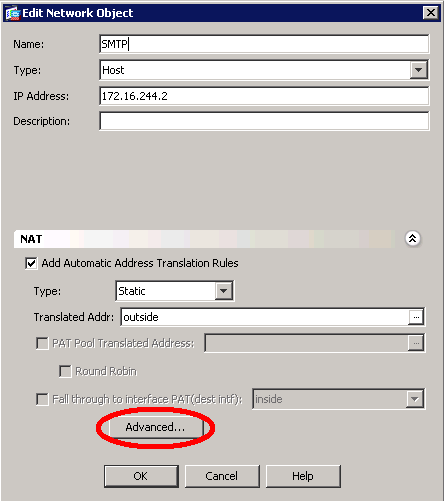
Step 2. Click Add, choose Network Object… (Found in the Right side panel)
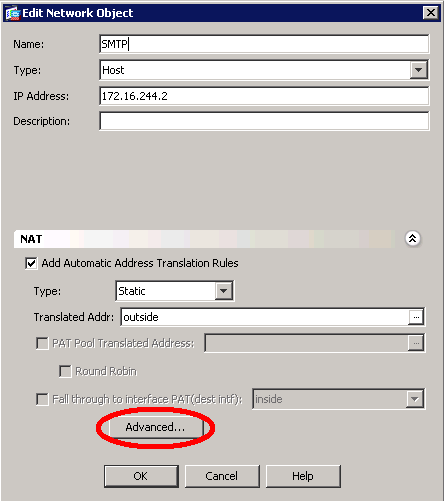
Step 3.
Ip address: type the Inside ipaddress of the pc/server
check Add Automatic Address Translation Rules
Type: static
Translated Addr: choose the WAN interface (default it is outside)
Click Advanced
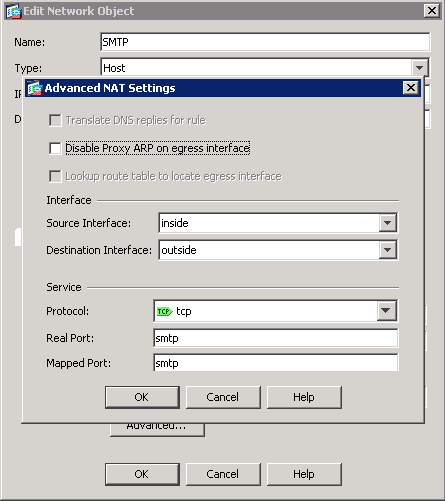
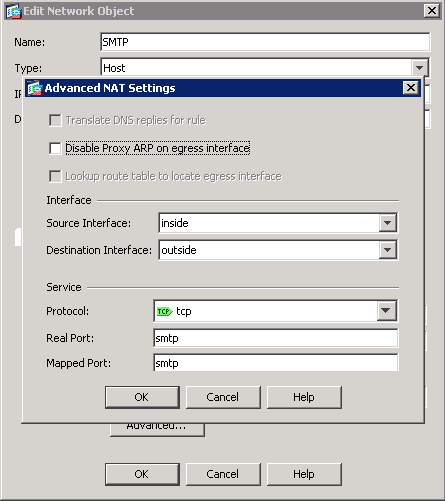
Step 4.
Souce Interface: Choose the interface which the pc/server is connected
Destination Interface: Choose the WAN interface (default it is outside)
Protocol: tcp
Real Port and Mapped Port: Type smtp og the port nummer your want to open
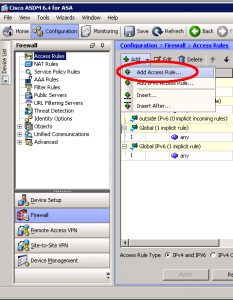
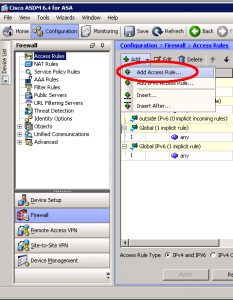
Step 5. Create a Access Rule, click Add, and choose Add Access Rule…
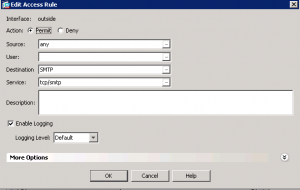
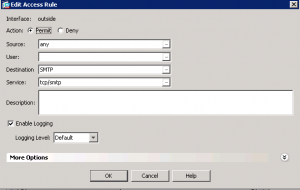
Step 6.
Interface: Outsite
Action: Permit
Source: Any
Destination: The object we just created